Enterprise Licenses Only
#
This plugin allows you to delegate access of OAuth providers. On the CrushFTP's login page next to the login button will appear the enabled provider's "Signed in" button".Currently Google Sign-In, Microsoft Sign-In and Azure Active Directory B2C Sign in are supported.
1. Google Sign-In
#
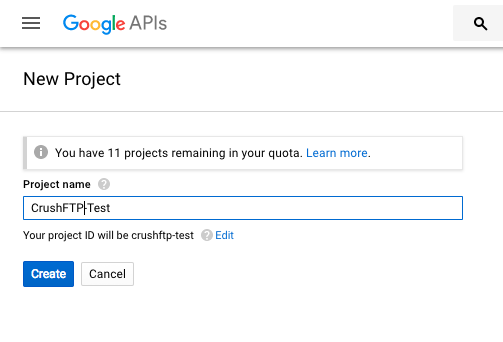
You will start at the API credentials manager:
https://console.developers.google.com/projectselector/apis/credentials

You first need to make a project. My example calls this CrushFTP-Test.
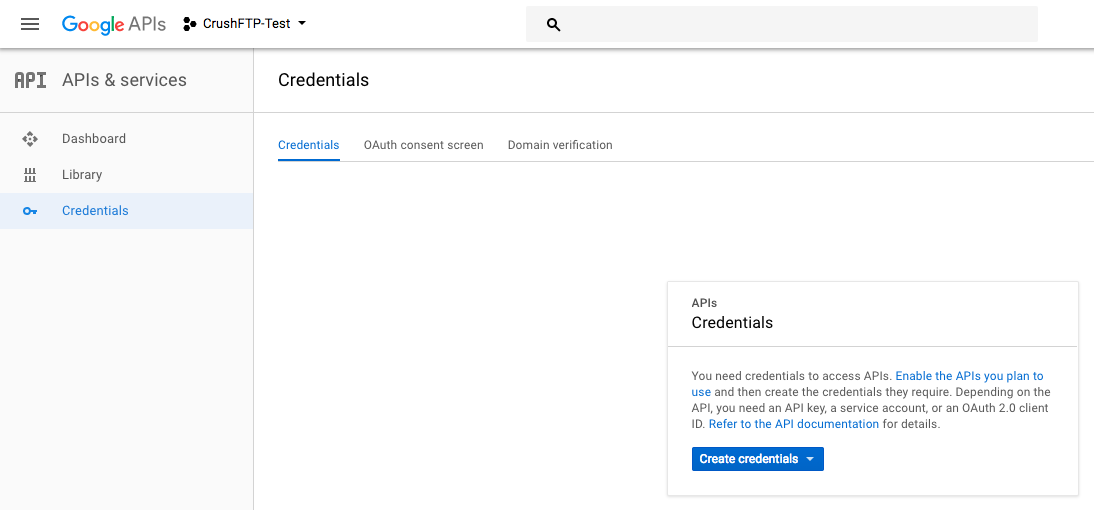
Next select create credentials, and choose the Web Application type.
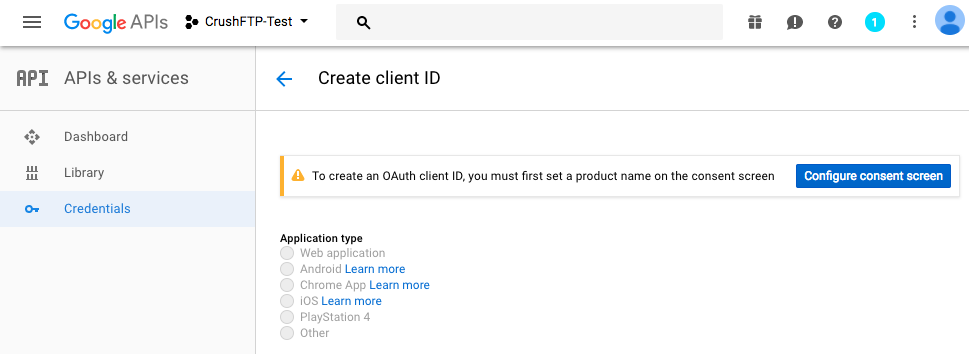
When configuring the credential, you have to tell Google the domain you will be originating from when creating the auth token, so this is the URL you use for server administration. Just the protocol://dns_or_ip:port Don't have a trailing slash or it will complain.
You also need to put in the redirect URL of where Google is going to send back the Id token (Id Token : That will be used for authentication of the google user). Copy the Client ID that will be required to integrate the Google Sing-In Button.
Integrate Google Sign-In button
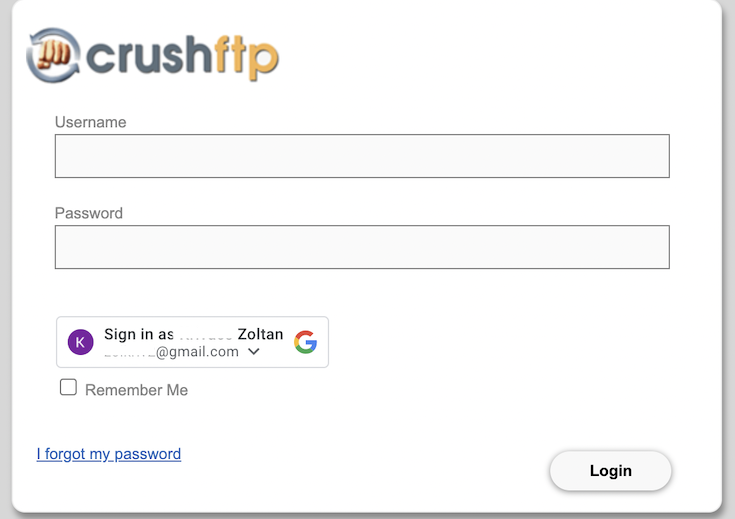
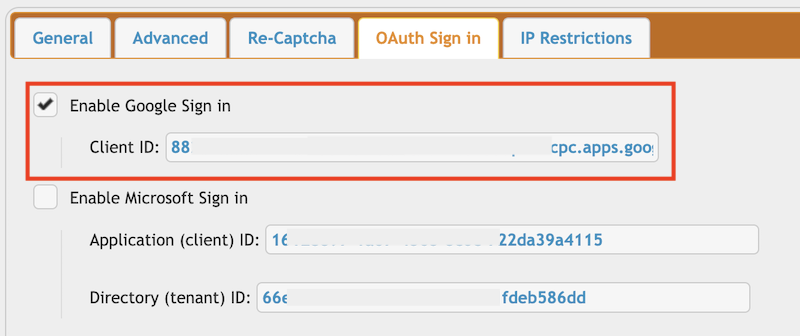
Go to the Preferences-> Ip/Servers and select the HTTP or HTTPS port item (OAuth Sign In Tab) where you want to enable the Google Sing-In button. Check the "Enable Google Sign in" flag and provide the Client ID of you Google project(mentioned above).
2. Microsoft Sign-In
#
It requires Microsoft Graph Application registration. Start at the Microsoft azure portal:
https://azure.microsoft.com/en-us/features/azure-portal/

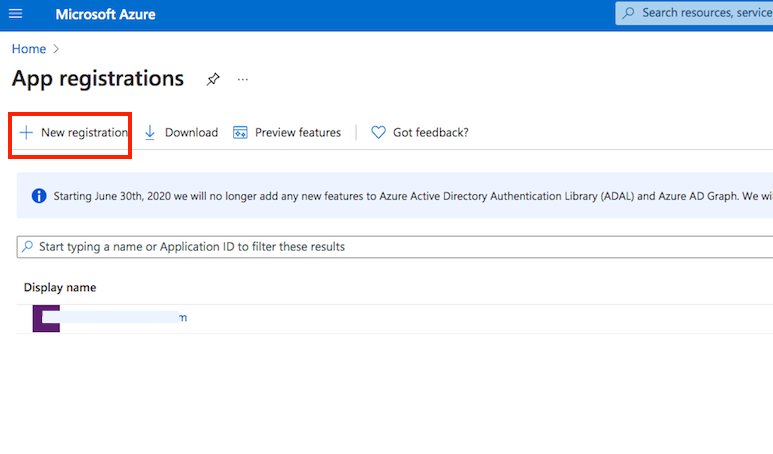
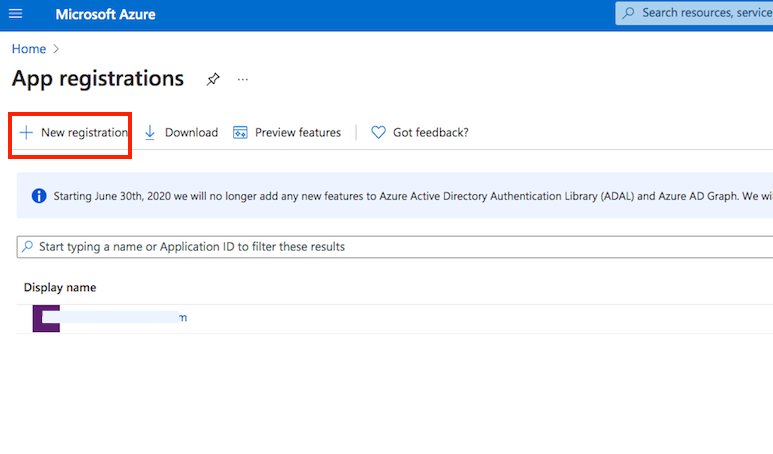
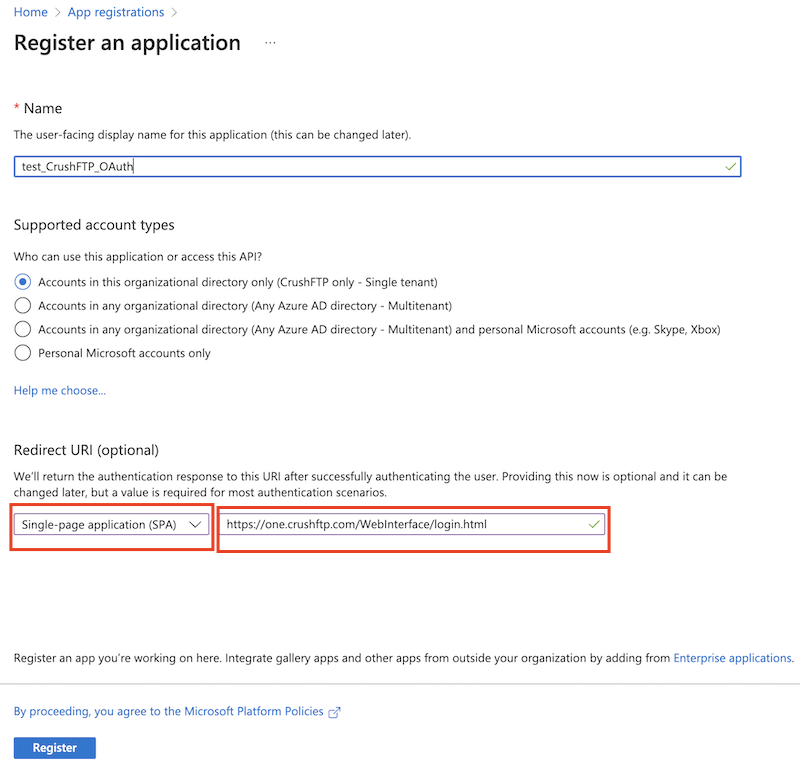
Application registration: Go to the App registrations and click on New registration:
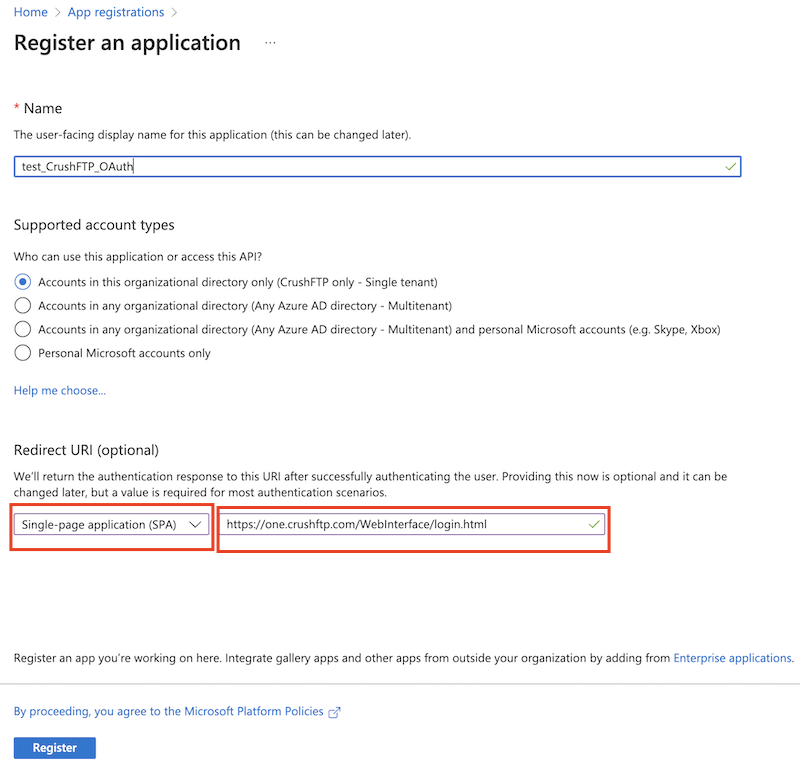
Name it. Select Single-page Application as platform. The redirect url must ends with :WebInterface/login.html. Then click on register.
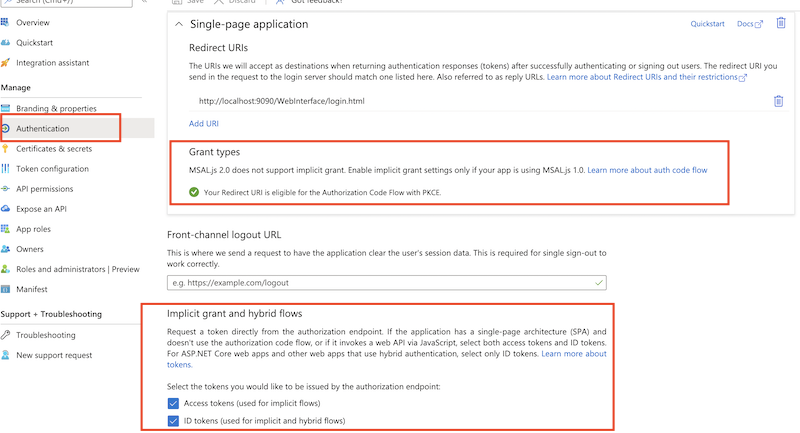
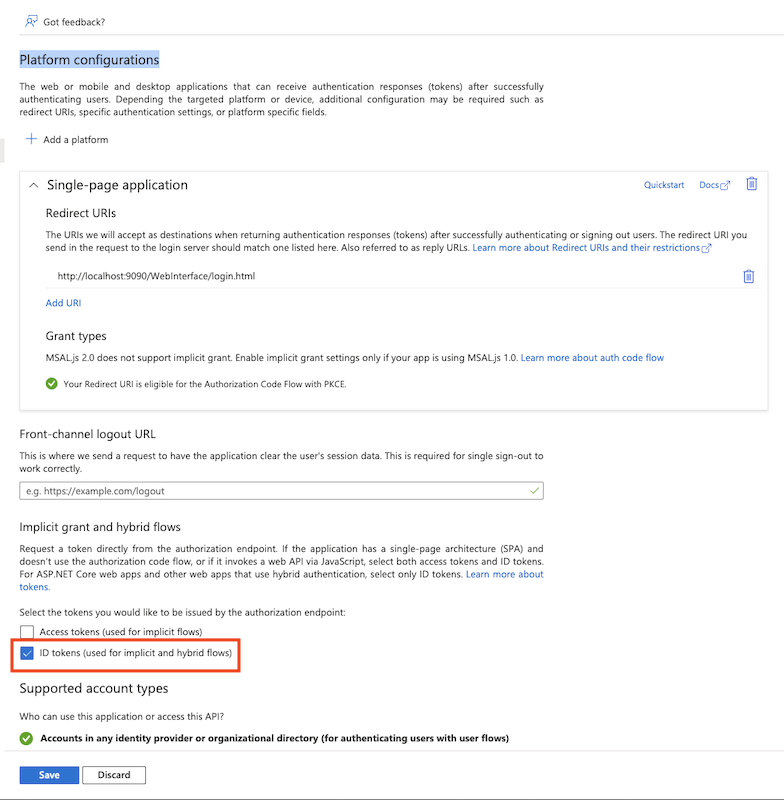
Make sure that MSAL.js 2.0, Implicit grant (Access Token, ID Token) grant types are permitted.
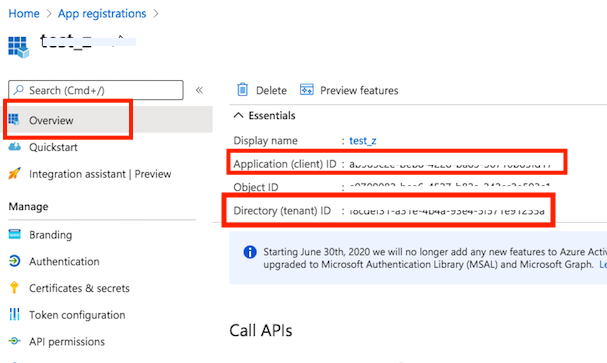
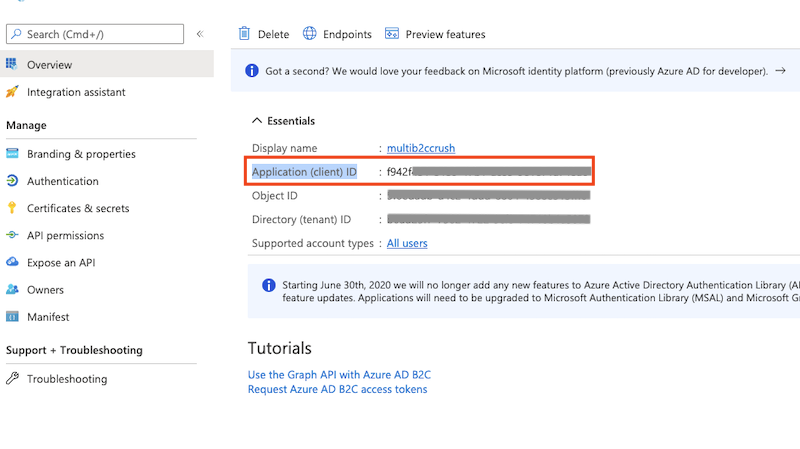
Get Client Id and Tenant Id from App registration -> Overview.
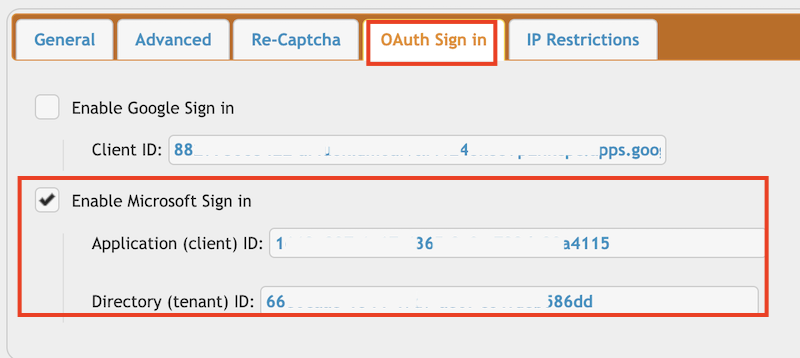
Go to the Preferences-> Ip/Servers and select the HTTP or HTTPS port item((OAuth Sign In Tab) where you want to enable the Microsoft Sing-In button. Check the "Enable Microsoft Sign in" flag and provide the Client ID and Tenant ID of your App registration(mentioned above).
3. Azure Active Directory B2C
#
About Azure Directory B2C : https://docs.microsoft.com/en-us/azure/active-directory-b2c/overview

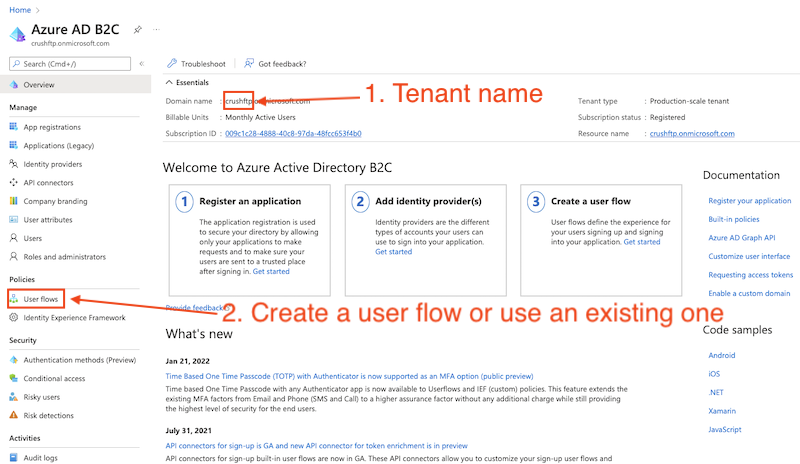
CrushFTP requires : Tenant name, User flow name, Client ID of the App registration.
Application registration: Go to the App registrations and click on New registration:
Name it. Select Single-page Application as platform. The redirect url must ends with :WebInterface/login.html. Then click on register.
Check the flag "ID tokens (used for implicit and hybrid flows)" at Platform configurations.
Get Application (client) ID from App registration -> Overview
Go to the Preferences-> Ip/Servers and select the HTTP or HTTPS port item((OAuth Sign In Tab) where you want to enable the Azure Active Directory B2C button. Check the "Enable Azure Active Directory B2C Sign in" flag and provide the Tenant name, User flow name, Client ID of the App registration (mentioned above).
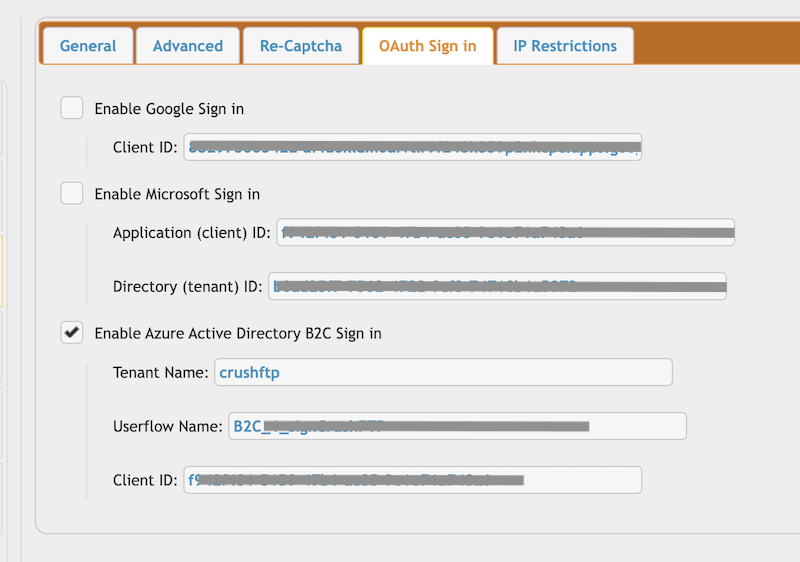
Configure the CrushOAuth plugin and enable the flag: "Enable Azure Active Directory B2C Auth".
4. Plugin Settings
#
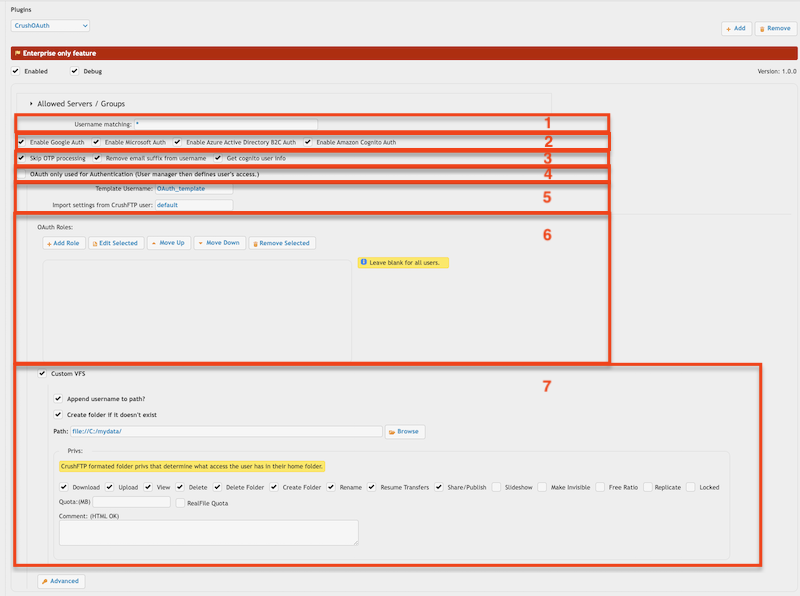
1. Username matching -> It filters the OAuth user name (Google Auth: email address, Microsoft Auth: user principle name). You can put multiple value separated by comma. Domain filter is allowed to (like *mydomain.com).
2. Allowed authentication types
3. OAuth only used for Authentication (User manager then defines user's access.) -> If the users already exists with username of the OAuth, you can use the plugin just for authentication.
4. Template Username -> The signed in user inherits no just the settings, but the VFS items too (as Linked VFS).
Import settings from CrushFTP user -> The signed in user inherits just the settings from this user.
5. VFS related settings : You can also assign a VFS item for the signed in user.
Add new attachment
Only authorized users are allowed to upload new attachments.
List of attachments
| Kind | Attachment Name | Size | Version | Date Modified | Author | Change note |
|---|---|---|---|---|---|---|
png |
app_reg_auth_config.png | 160.8 kB | 1 | 11-Feb-2022 03:18 | krivacsz | |
png |
app_reg_config.png | 173.1 kB | 1 | 11-Feb-2022 03:10 | krivacsz | |
png |
b2c_azure_settings.png | 184.4 kB | 1 | 13-Jul-2022 05:39 | krivacsz | |
png |
b2c_client_id.png | 127.2 kB | 1 | 13-Jul-2022 06:01 | krivacsz | |
png |
b2c_id_token.png | 207.0 kB | 1 | 13-Jul-2022 05:49 | krivacsz | |
png |
cognito_client_id_secret.png | 66.4 kB | 2 | 21-Nov-2022 04:11 | krivacsz | |
png |
cognito_user_pool.png | 82.3 kB | 2 | 21-Nov-2022 04:07 | krivacsz | |
png |
cognito_user_pool_app_client_1... | 244.9 kB | 1 | 07-Sep-2022 03:29 | krivacsz | |
png |
cognito_user_pool_app_client_2... | 340.5 kB | 1 | 07-Sep-2022 03:29 | krivacsz | |
png |
dmz_template_user_internal_por... | 94.7 kB | 1 | 13-Sep-2023 06:21 | krivacsz | |
png |
g_sign_origin_redirect_url.png | 85.4 kB | 1 | 19-Nov-2022 08:24 | krivacsz | |
png |
gsign_in_button.png | 204.4 kB | 1 | 23-Aug-2021 16:11 | krivacsz | |
png |
http_port_oauth_item_settings.... | 43.5 kB | 1 | 13-Sep-2023 05:43 | krivacsz | |
png |
plugin_settings.png | 99.6 kB | 7 | 17-Feb-2023 10:22 | krivacsz | |
png |
port_item_settings.png | 76.4 kB | 2 | 11-Feb-2022 02:41 | krivacsz | |
png |
port_item_settings_b2c.png | 105.6 kB | 1 | 13-Jul-2022 06:29 | krivacsz | |
png |
port_item_settings_cognito.png | 14.1 kB | 2 | 07-Sep-2022 04:24 | krivacsz | |
png |
port_item_settings_ms.png | 75.3 kB | 1 | 11-Feb-2022 03:35 | krivacsz |
«
This particular version was published on 13-Jul-2022 06:45 by krivacsz.
G’day (anonymous guest)
Log in
JSPWiki